A RAID log is a document used by project managers, business analysts, risk managers, team leads, and executives to help with project risk management by summarizing the following key pieces of information:
- Risks
- Assumptions or actions
- Issues
- Dependencies or decisions
As a project manager, you can use a RAID log to keep your stakeholders—and yourself—straight on the latest project deets. When executed well, this log can act as a key strategy document for summarizing project health at the leadership level.
RAID logs are often used in conjunction with risk management software.
What Is a RAID Log and What Does ‘RAID’ Stand For?
RAID stands for: risk, assumptions (or actions), issues, and dependencies (or decisions).
| RAID Log Component Definition | Examples |
|---|---|
| Risks. Identify and categorize risks and opportunities, their probability of occurrence, their impact/severity should they occur, and the mitigation plan and actions | -Risk: Inclement weather delays data collection schedule |
| Assumptions or Actions. Document project parameters to prevent scope creep; maintain a “to do” list based on ongoing project work | -Assumption: required resources are available to execute project work -Action: engage with finance team for a cost breakdown of existing third party suppliers |
| Issues. Document events that have occurred that impact project progress and explain the path to resolution | -Issue: A security breach compromises the integrity of customer data |
| Dependencies or Decisions. List activities that cannot be started or completed without another activity being started or completed; document previously agreed upon courses of action and the rationale for pursuing or failing to pursue them | -Dependency: conduct alternatives analysis prior to procuring new vendor management system -Decision: build in-house talent management system to maintain focus on high-performance culture, even though this will be more costly in the short-term |
You’ll see that the definition of RAID includes some dual acronyms: assumptions or actions, dependencies or decisions. Here are my hot takes on how to approach these:
- Assumptions vs. Actions. I can’t tell you how many times having a list of assumptions stopped scope creep in its tracks. If you’d like to keep your log geared towards a senior audience, I’d recommend keeping action items in a separate document focused on tactical execution.
- Decisions vs. Dependencies. In my experience, no one ever remembers why decisions were made: specifically, the alternatives considered but rejected and the reasons why. To avoid circular thinking over the course of a lengthy engagement, I’d recommend documenting decisions in your RAID log in addition to dependencies.
When Should You Create A RAID Log?
A RAID log should be created at the start of a project during the initiation or planning phase, once enough is known about scope, stakeholders, and objectives to identify initial risks and assumptions. From there, revisit it at major milestones, whenever scope changes, or any time a significant risk or issue emerges. On Agile projects, a natural update cadence is the start of each sprint.
RAID Log vs Risk Register
While there is some overlap between these two documents, the difference is that a RAID log is more comprehensive than a risk register. In addition to documenting risks, a RAID log also includes assumptions or actions, an issues log, and dependencies or decisions.
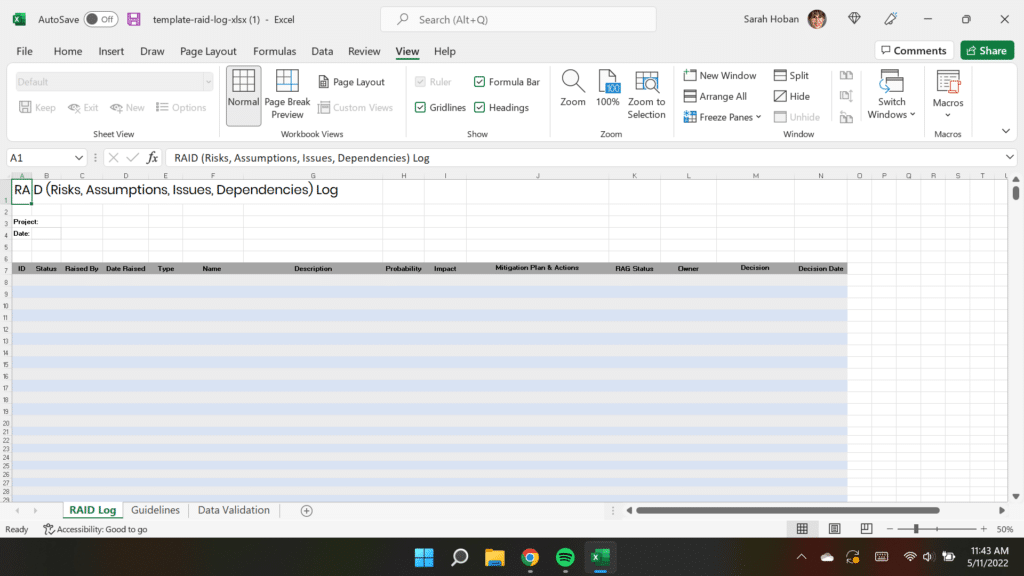
RAID Log Template
I’ve included a download of a RAID log template in Microsoft Excel (you'll need to be a DPM member to get the template). You can use this template to document risks, assumptions, issues, and dependencies. Columns M and N track decisions and the decision date.
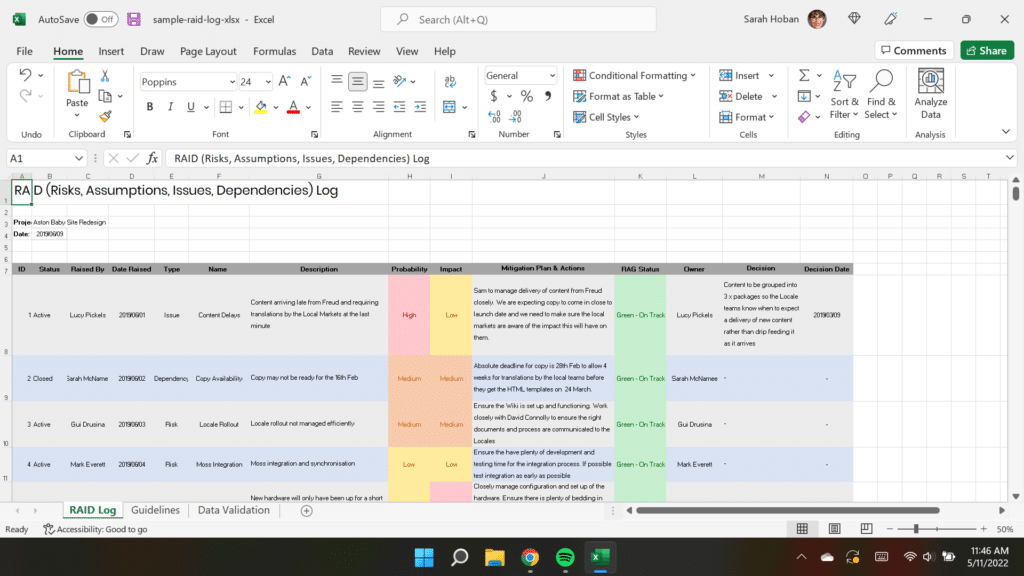
RAID Log Sample And Examples
In addition to the RAID log template, I’ve also included an example Excel log so you can get a feel for the finished product (you'll need to be a member to access this as well).
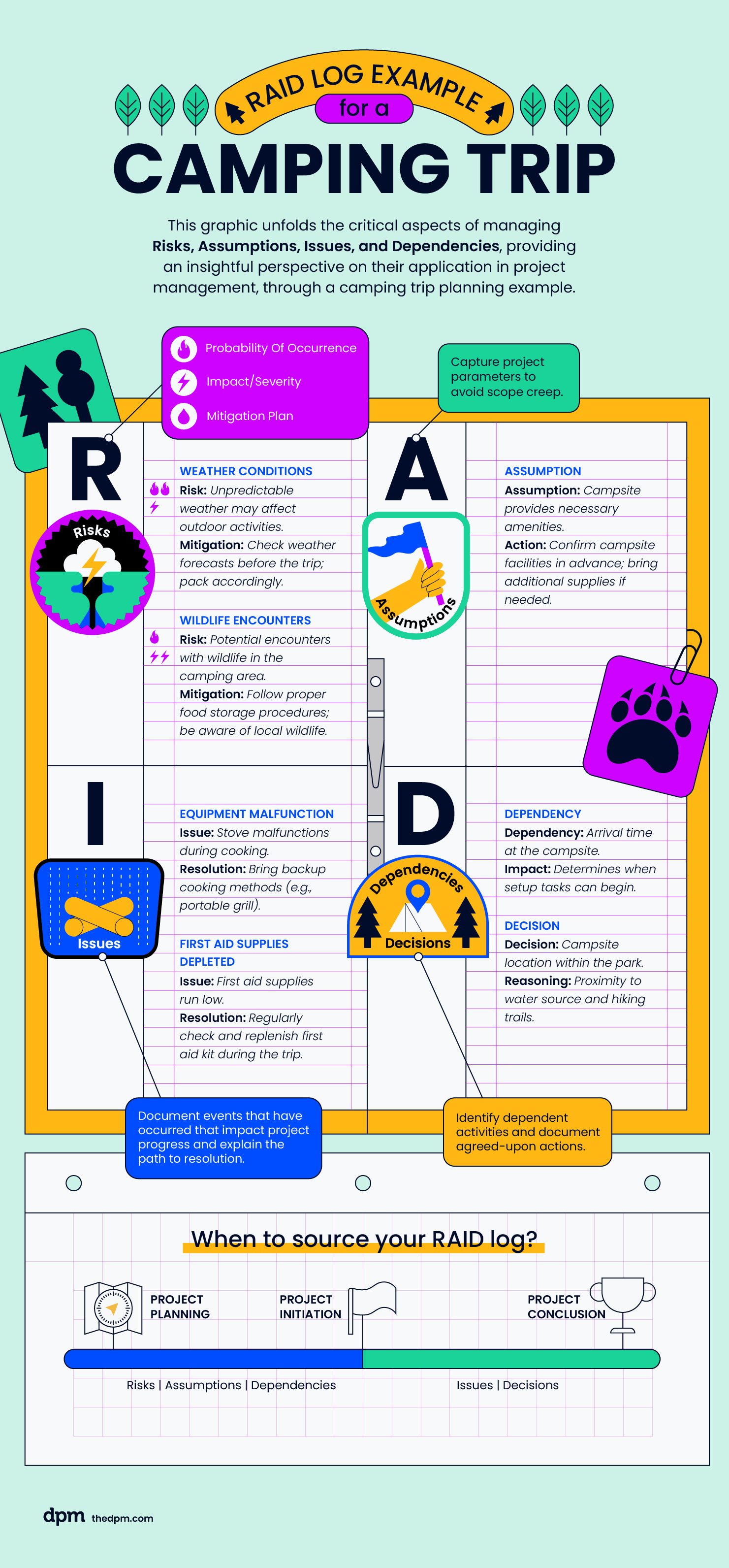
Here's another example, covering how RAID logs might be applied in a camping trip project scenario.
How To Create A RAID Log
Now that you’ve got your template ready to go, how exactly do you go about populating it? During the project planning phase, you’ll be able to source content for the following components of your RAID log:
- Risks
- Assumptions
- Dependencies
Actions, issues, and decisions don't come into play until after the project begins.
For each item you log, capture these fields at minimum:
- Description — a brief summary of the risk, assumption, issue, or dependency
- Owner — the person responsible for managing or resolving it
- Priority — high, medium, or low
- Status — open, in progress, or closed
- Target date — when it needs to be resolved or reviewed by
- Mitigation/action plan — the steps being taken to address it
Having consistent fields across every entry makes the log scannable for stakeholders and easier to maintain over time.
Potential Sources Of Content For A RAID Log
You can source content for your log from multiple channels:
- Stakeholder interviews
- Current or prior project documentation
- Examples: lessons learned template, retrospectives, post mortems, project charters, project plans, project schedules
- Prior experience executing similar projects
- Open source materials online
- Critical thinking based on information you’ve gleaned from the above sources (e.g., your stakeholders aren’t explicitly saying something is a pain point, but their reluctance to address the topic suggests this area would benefit from additional discovery.)
Best Practices
Once your project starts, and you’ve got your draft RAID log ready to go, keep in mind these best practices for how to use the log while managing your project:
- Tune to the appropriate level of detail for the audience. Stakeholders rely on the RAID log to understand the context for this project and any risks or issues that may threaten project success. Keep the focus on business impacts, rather than tactical updates that may not be meaningful to someone who is not engaged in the day-to-day.
- Monitor and update the log throughout the project lifecycle. This artifact is useless if you don’t update it and feed it through other documentation like a decision log. That’s another reason to keep the content concise so that the document is not onerous to maintain. Most of your time should be spent unblocking problems, rather than documenting them.
Benefits
RAID logs benefit stakeholders, project team members, the business, and you as the project manager.
- It's a one-stop-shop for pertinent project information that readily offers real-time insights into project health
- It offers the ability to track risks before they become issues, and then quickly triage issues if risks are realized
- Project managers can document assumptions and decisions to mitigate the risk of having to backtrack on discussions that may delay the project.
How Are RAID Logs Used In Agile?
Typically, agile projects tend to shy away from documentation in favor of developing a working product. That being said, I’d contend that developing a RAID log is worth the extra effort.
The reason? Agile projects typically follow an iterative approach to project execution that invites greater experimentation. This approach is great for failing fast to generate learnings more quickly.
Yet, destigmatizing failure introduces additional risks that could derail your project. And, an organization can only learn from failure if it documents the assumptions and decision-making that informed each experiment.
What’s Next?
If you need more help with risk management, consider taking our Mastering Digital Project Management course. In addition to risk management, you'll also learn about managing projects throughout the entire project life cycle, from initiation to project closure.




